Moonshadow
Computer science professor James O’Brien began tinkering with code while in elementary school—thanks to his father, who let him play text-based adventure games online. During one game, he rewrote the code to get past a pesky dragon.
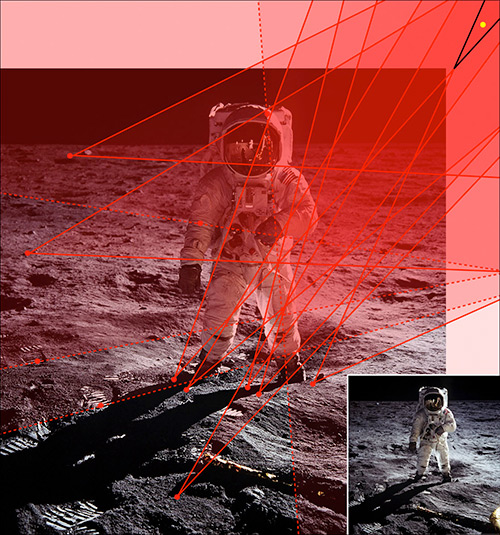
SHOOTING THE MOON: James O’Brien, professor of computer science, uses this iconic 1969 moon-landing photograph to demonstrate a photo forensics tool he helped develop. The tool determines whether a photograph has been altered by analyzing its shadows for light source inconsistencies. (Original image © 1969, NASA. Annotated image by Kee, O’Brien and Farad, 2012)
That curiosity and experimentation eventually landed O’Brien a career in computer graphics. Not only has he helped develop methods for creating realistic simulations of material fracturing and explosions used in movie and video game special effects, but he also helped design a technique for detecting altered photographs.
“The widespread use of tools like Photoshop makes it easier than ever to manipulate photographs and makes the public less trustful of photographic reality,” says O’Brien. “Faked photographs have real-world consequences.”
He cites one of many possible examples: a 2004 photographic mash-up that implied then-presidential candidate John Kerry attended the same 1960s anti-Vietnam War event as activist- actor Jane Fonda.
“How many votes did that cost him, even after the manipulation was exposed?” asks O’Brien.
To uncover such manipulations, the team developed a photo forensics tool for analyzing shadow inconsistencies. It assumes a single point light source, such as a table lamp, or as in this iconic 1969 moon-landing photograph, the sun, which casts harsh shadows on the uneven lunar surface.
Sudoku strategy
Their technique creates a set of imaginary lines, or cones, extending from points in a photograph’s various shadows—in this case, those cast by the astronaut or on the astronaut—through the shadow-casting parts of the figure and onto the implied light source. If all the imaginary lines or cones connect from their shadow origin points to the same light source, that is significant evidence that the photograph was not manipulated.
O’Brien likens it to a Sudoku puzzle in which the requirement that each line has the same sum creates a set of constraints for solving the puzzle.
“While any one specific method for detecting manipulation can be fooled,” says O’Brien, “our goal is to gradually build up a whole toolkit to test all aspects of the photograph.”